Blog
An Update on the LinkedIn Data Breach
August 24, 2021
Social media can be a playground for cybercriminals. These thieves have become so sophisticated, they can glean your personal data from sites without even hacking into a system. This is […]
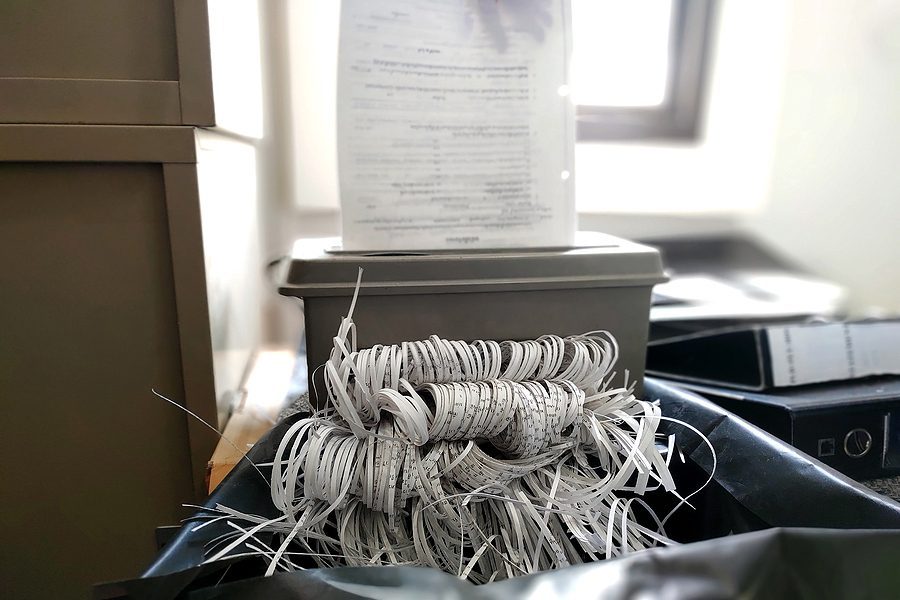
Partnering with a Data Destruction Service Can Increase Productivity
July 27, 2021
Some small and mid-sized businesses assume that managing their data destruction services in-house will save them money. It seems feasible that someone on the staff can take care of document […]
Are Your Remote Employees Careful Enough with Company Information?
July 23, 2021
Some businesses have allowed employees to work remotely for years, while others were thrust into this new reality without preparation. No matter what the circumstances, remote workers come with an […]
Choose the Right Corporate Data Destruction Service for Your Business
June 21, 2021
Most businesses understand the need for shredding their sensitive documents. Some businesses will attempt to handle their shredding needs in-house, but this comes at a much greater security risk. In-house […]
Benefits of an Internal Data Privacy Assessment
June 14, 2021
Many small businesses think that they are at a lower risk for a data breach due to their size or the nature of their business. However, a business of any […]
Personal Information Exposed Through Recent Geico Data Breach
May 24, 2021
The risk of a data breach is always looming, and this was once again brought to everyone’s attention by a large company under cyber-attack. Geico was the target of a […]
Short Term Remote Work Requires Secure and Responsible E-Waste Destruction
May 18, 2021
E-waste is the aftermath created by discarded electronics. With short-term remote work happening on a grand scale, companies need to be diligent and responsible when disposing of the excess electronics […]
Data Breaches Can Happen On and Off Line. Is Your Business Ready?
April 28, 2021
In the digital world we are living in, hacking and cyber-attacks are a constant threat to businesses big and small. You need to keep your client’s sensitive information safe. But […]
Can You Afford a Data Breach?
April 15, 2021
No matter how big or small your business, the cost of a data breach is high. Every business is at risk of a data breach, and criminals are consistently figuring […]
5 Things You Can Do to Protect Your Business from a Data Breach
March 29, 2021
As a small business, you may not believe that you are at risk of a security breach, because you can’t imagine who would want to target you. Small businesses often […]